
In earlier insights, we explored when risk forms, why inventory only exists while continuously constrained, why location must be proven first, and why documentation must be bound to verified existence. This piece moves one step deeper: even when facilities, inventory, and documentation are verified, verification itself cannot persist without persistent identity.

Facilities and inventory are verified continuously through inspections, operational processes, and formal documentation. Inspectors attend sites, operators produce reports, auditors assess controls, and institutions rely on these records to make operational and financial decisions. These activities create verification events that confirm what was observed at a specific moment in time.
Verification exists.
What does not exist is a persistent identity.
Each verification event exists as an individual record rather than as part of a continuously recognisable identity that endures beyond the moment of observation. Inspection reports, certificates, and audit confirmations describe what was true at a point in time, but they do not establish a continuously verifiable identity that can be relied upon without repetition.
As a result, verification must be recreated repeatedly. It does not accumulate into a continuously enforceable state.
Verification exists — but it does not persist.
Verification records what was true.
Identity allows verification to endure.
Facilities are referenced in many ways: by name, by address, by coordinates, by operator systems, and by inspection documentation. These references allow infrastructure to be described and located, but they do not establish persistent identity in a machine-verifiable sense.
References can change. Names can be reused. Addresses can be imprecise. Coordinates describe location, but they do not verify the infrastructure within it. Documentation may continue to exist even when the physical conditions it describes have changed.
These references allow infrastructure to be described. They do not allow infrastructure to be persistently recognised.
Identity requires continuity. References alone do not provide it.
References describe infrastructure.
Identity allows systems to recognise it over time.
When identity does not persist, verification cannot persist either. Each inspection confirms conditions at a particular moment, but it does not create a continuously verifiable identity that remains valid as physical conditions evolve.
Physical infrastructure exists within dynamic environments. Facilities are modified. Structural conditions change. Operational controls weaken or strengthen. Inventory moves. External risks evolve continuously.
Verification remains fixed at the moment it was recorded, while the physical reality it describes continues to change.
Without persistent identity, verification becomes historical rather than continuously enforceable.
Because infrastructure lacks persistent identity, verification cannot be relied upon indefinitely. Each participant in the ecosystem must independently re-establish the same truth before relying upon it.
Inspectors revisit sites. Auditors repeat assessments. Banks reassess collateral. Operators regenerate reports. Each party recreates verification that has already occurred, not because verification was inadequate, but because verification cannot persist without a persistent identity.
Without identity, verification cannot accumulate.
Trust must be recreated repeatedly, rather than persist continuously.
Without a persistent identity, verification resets.
With persistent identity, verification compounds.
Physical infrastructure exists in dynamic environments. Facilities evolve. Layouts change. Operational conditions shift. Inventory moves. Risk evolves continuously.
Verification remains static.
Inspection reports, audit records, and documentation capture conditions at specific moments, but they do not adapt as physical reality changes.
Static verification applied to dynamic infrastructure cannot create persistent trust. It can only describe what was true previously, rather than continuously confirm what remains true.
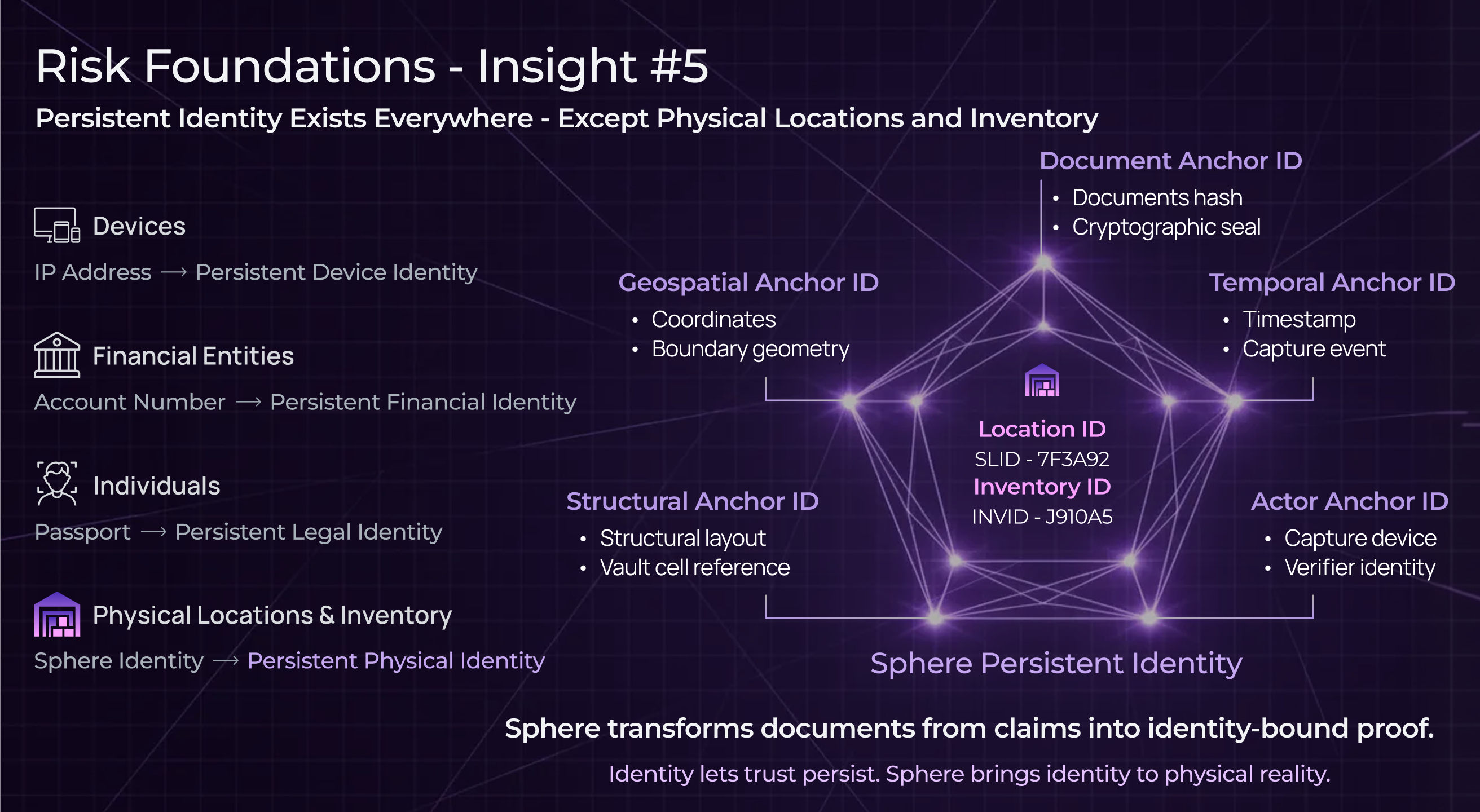
Every mature digital system begins with identity. Identity allows systems to recognise entities consistently across time. It allows verification events to accumulate rather than exist in isolation. It allows trust to persist rather than reset.
Identity provides the foundation for persistence across every mature system:
These identifiers allow systems to recognise entities continuously, allowing actions, records, and verification to persist rather than reset.
Physical infrastructure has no equivalent identity layer.
Without a persistent identity, verification remains episodic. With persistent identity, verification becomes cumulative.
Persistent identity allows verification to become independently and continuously verifiable. Systems no longer rely solely on human interpretation of reports and documentation. Instead, verification can be confirmed programmatically, allowing systems to recognise facilities, associate verification with specific structural boundaries, and continuously confirm that verification remains bound to physical reality.
Verification does not fail because inspections stop.
Verification fails because the identity does not persist.
This transition does not require more inspections, more documentation, or more manual review. It requires establishing a persistent identity for physical infrastructure — an identity that binds verification to facilities, structural boundaries, and physical reality continuously over time.
When identity persists, verification can persist. When verification persists, trust can persist.
Trust becomes structural rather than assumed.
Facilities and inventory are verified every day. What is missing is not verification — it is persistent identity.
Without persistent identity, verification remains temporary, trust remains episodic, and reality must be rediscovered repeatedly. When infrastructure can be persistently recognised, verification becomes continuous rather than episodic, and trust becomes structural rather than assumed.
Persistent identity allows verification to endure.
Disclaimer
This article is intended for general informational and educational purposes only. It discusses observed industry patterns and structural risk considerations and does not constitute legal, financial, or investment advice. References to losses or failures are illustrative and non-exhaustive, and do not refer to any specific organisation unless expressly stated.